Hacking and IT intrusions are no longer just one breach vector among many—they are the dominant cause of reportable incidents and by far the most expensive to remediate. Theft, loss, and improper disposal still occur, but they have become statistical noise next to the scale and impact of cyberattacks.
This blog summarizes key findings from a deeper quantitative analysis of the OCR breach portal (last 24 months) and highlights the business and regulatory implications for healthcare leaders. For a complete breakdown of the data, methods, and cost model, see the full whitepaper: “The Real Cost of Healthcare Data Breaches: An Analysis of HHS OCR Data (2024–2025)”.
Download the full whitepaper: “The Real Cost of Healthcare Data Breaches (2024–2025)”
1. What the OCR Breach Data Shows
The OCR breach portal tracks “large” breaches (500+ individuals affected) reported by covered entities and business associates. Looking across the last two years of entries:
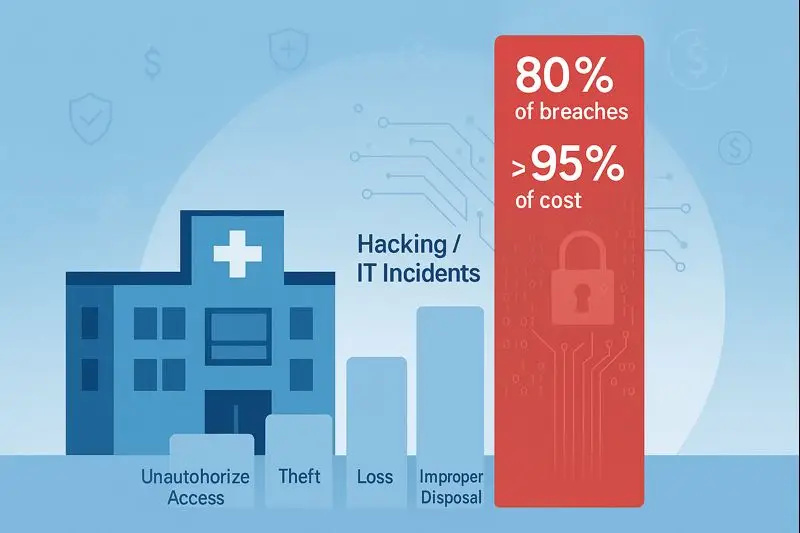
Hacking/IT incidents account for roughly 80% of all reported breaches.
Unauthorized access or disclosure accounts for roughly 15–16%.
Theft, loss, and improper disposal together make up only a few percent of cases.
In other words, four out of five reportable healthcare breaches are now driven by malicious cyber activity—network intrusions, ransomware, compromised credentials, or related IT incidents.
The pattern is equally stark when looking at the number of records:
Hacking incidents routinely involve very large data sets (hundreds of thousands to millions of records).
Insider or misdirected disclosures typically affect thousands or tens of thousands of records.
Loss/theft/disposal incidents are usually limited to thousands of records at most.
From a pure frequency standpoint, the modern healthcare breach is overwhelmingly a cyber event, not a lost laptop or a box of paper charts in a dumpster.
2. The Economics of a Healthcare Breach
Each reported breach triggers a predictable set of cost drivers, regardless of vector:
Technical investigation and forensics
Identifying how the breach occurred, stopping it, and ensuring attackers are not still present. This includes log analysis, endpoint and network forensics, and sometimes rebuilding systems.Notification and credit monitoring
Notifying affected individuals, regulators, and sometimes the media; setting up call centers; and often providing credit monitoring or identity protection. Costs scale almost linearly with the number of individuals affected.Regulatory penalties and corrective action
OCR enforcement can include civil monetary penalties, corrective action plans, and independent monitoring. For serious violations, HIPAA fines can reach into the millions of dollars per incident.Legal costs and settlements
Class actions and state investigations now commonly follow large healthcare breaches. Defense costs, settlements, and fee awards for plaintiffs’ counsel significantly increase the total impact.Remediation and security upgrades
Implementing new security controls, replacing or re-architecting systems, and investing in tooling and expertise that should have been present before the incident.Reputational damage and lost business
Patient churn, reduced referrals, contract terminations, and lost future business. This component is difficult to measure but often the largest in the long term.
These cost drivers exist across all breach vectors, but the scale and regulatory posture differ sharply between a major cyber incident and a small internal mistake.
3. Why Hacking/IT Incidents Dominate Total Cost
3.1. Scale: More People, More Notifications, More Lawsuits
Hacking incidents consistently affect the largest populations. A single network intrusion can expose millions of records across multiple facilities, business lines, or covered entities. Notification and call-center operations for a multi-million-person breach can alone cost millions of dollars.
By contrast:
A typical unauthorized disclosure incident might involve a misdirected email, an employee misusing access to view a few hundred or a few thousand records, or a partner misconfiguration affecting a narrower population.
Loss/theft/disposal incidents often involve a small number of devices or boxes of records, constraining their scope.
When notification costs, legal exposure, and reputational impact are all proportional to the number of affected individuals, the largest category by scale will almost always dominate the economic impact.
3.2. Regulatory Risk: Perceived Preventability and Systemic Failure
HHS OCR treats large hacking incidents as clear indications of systemic security failures: inadequate risk analysis, missing safeguards, poor patching and monitoring, or excessive privileges.
As a result:
Cyber events frequently lead to multi-year corrective action plans and multi-million-dollar settlements or penalties, particularly when encryption, MFA, segmentation, or basic logging were missing.
Theft and loss cases still draw fines (especially for unencrypted laptops or unprotected backup media), but they are now relatively rare and more often involve mid-six-figure rather than eight-figure resolutions.
Unauthorized access/disclosure cases often result in targeted corrective measures (training, policy updates, revised access controls); fines tend to be more modest unless the incident is large or persistent.
Regulators increasingly view large hacking incidents as both foreseeable and preventable, which raises the enforcement baseline.
3.3. Operational Disruption and Patient Safety
Ransomware and destructive attacks carry a cost category that theft/loss incidents generally do not: extended downtime.
When a major hospital or health system loses electronic health record (EHR) access, e-prescribing, imaging systems, or revenue-cycle systems for days or weeks, the consequences are severe:
Deferred or canceled procedures and visits
Manual workarounds that reduce throughput and increase error risk
Delayed billing, claims, and revenue recognition
Potential patient harm, which may itself result in litigation
A single large ransomware event can cost tens of millions purely in lost revenue and recovery efforts, even before considering notification, legal, and regulatory costs.
4. How Other Vectors Compare
Although hacking/IT incidents dominate the aggregate picture, the remaining vectors still matter at the entity level.
4.1. Unauthorized Access/Disclosure
These cases typically involve:
Employees snooping on records without a legitimate need
Misaddressed emails or faxes
Partners mishandling or misconfiguring shared data
They are generally smaller in scale, and technical remediation is less complex. However:
OCR can and does fine organizations for repeated insider snooping or for failing to implement and enforce role-based access controls.
Some large “unauthorized disclosure” events (e.g., misuse of web tracking pixels) have affected millions of individuals and led to multi-million-dollar settlements.
For many organizations, this category represents manageable but persistent “background noise” risk that still adds up in legal, compliance, and operational terms.
4.2. Theft, Loss, and Improper Disposal
These vectors have become rare, largely due to:
Device encryption
Better media-handling procedures
Increased awareness of physical security
When they do occur, they tend to share several characteristics:
Scope in the hundreds or low thousands of records
Straightforward notification and remediation
Fines concentrated around clear policy failures (e.g., unencrypted laptop, discarded paper records)
Individually, these breaches can be painful—especially for smaller organizations—but collectively, across the entire sector, they represent a small fraction of the total cost burden compared to cyberattacks.
5. Estimated Cost by Vector (Two-Year View)
Using conservative industry-average cost-per-breach estimates and the observed frequency of each vector over the last two years, a high-level picture emerges:
Hacking/IT incidents
Roughly four out of five breaches
Typical total cost per incident in the mid- to high-single-digit millions; many at eight figures
Aggregate cost across the sector over two years likely in the low tens of billions of dollars
Unauthorized access/disclosure
Approximately one in six breaches
Costs usually in the low- to mid-single-digit millions, with outliers higher
Aggregate cost in the hundreds of millions
Theft, loss, improper disposal
Only a few dozen incidents across the entire country over two years
Costs often in the hundreds of thousands or low millions per incident
Aggregate cost in the tens of millions
From a portfolio perspective, hacking/IT incidents are responsible for the overwhelming majority of economic loss, both in direct expenditures and in long-term business impact.
6. Strategic Implications for Healthcare Leaders
For boards, CEOs, CIOs, CISOs, and compliance officers, the implications of this analysis are clear:
Prioritize controls and investments that directly reduce exposure to cyber intrusion.
Traditional safeguards around device encryption and paper records are still necessary, but marginal dollars should increasingly flow to controls that reduce the likelihood and impact of large hacking incidents: strong identity and access management, continuous monitoring, vulnerability management, network segmentation, and hardened third-party connectivity.Design architectures that limit “blast radius” by default.
The economic story of the OCR data is fundamentally a story about blast radius: large, centrally accessible datasets drive catastrophic cost when breached. Architectures that shard sensitive data, enforce strict access boundaries, and keep servers blind to full-context plaintext can materially change the risk curve.Recognize that business and regulatory costs compound.
It is no longer sufficient to think in terms of “IT cleanup costs” alone. Large cyber events trigger layers of cost—technical, legal, regulatory, reputational—that interact and compound over years. When modeling ROI for security and architectural transformation, these multi-year, multi-layer costs should be explicitly quantified.Treat third-party and ecosystem risk as first-class.
Several of the most impactful recent incidents originated not in a hospital or health system, but in a shared technology or service provider. Vendor security posture, contractual controls, and technical isolation are now as important as internal controls.
7. What the Full Whitepaper Covers
This blog provides a high-level narrative of the findings. The full whitepaper, “The Real Cost of Healthcare Data Breaches: An Analysis of HHS OCR Data (2024–2025)”, goes significantly deeper, including:
A detailed breakdown of breach counts and records affected by vector and year
A cost model that maps OCR portal data to per-incident and aggregate financial impact
Case studies of high-impact outlier events (including major ransomware and third-party breaches)
A decomposition of costs into technical, regulatory, legal, and business components
Strategic recommendations for reducing both likelihood and blast radius, including architectural patterns that keep servers from ever holding full-context plaintext
Download the full whitepaper: “The Real Cost of Healthcare Data Breaches (2024–2025)”
For organizations that manage large volumes of PHI, these findings support a simple conclusion: the greatest financial risk lies not in rare edge cases, but in the routine structure of how data is stored, accessed, and processed today. Changing that structure—especially for data in use—is where the next meaningful reductions in breach impact will be found.