Most security programs still organize around the idea of a “front door”: the application login, the perimeter, the API gateway. But the highest-impact incidents increasingly begin somewhere else—inside trust planes: identity systems, workflow automation, third-party integrations, and data movement pipelines that are explicitly designed to be trusted.
That is the modern failure mode: the attacker does not defeat your defenses. They use your authorized pathways.
And when your architecture centralizes plaintext access in one place, trust-plane abuse becomes wholesale compromise.
Why this matters now
Three current patterns illustrate why “trusted infrastructure” has become the attacker’s preferred route:
-
Trusted automation as a phishing platform. Recent campaigns abused Google Cloud Application Integration to send phishing emails from a legitimate Google-originating address and route victims through Google-owned infrastructure to credential-harvesters—misuse, not a breach, but still effective.
-
Third-party risk is no longer an edge case. Verizon’s 2025 DBIR executive summary reports that third-party involvement in breaches doubled year-over-year (15% to 30%).
-
Vendor compromise produces downstream “real-world harm” data. The Ledger / Global-e incident is a representative example: name, address, email, phone, and order details—exactly the dataset attackers use for targeted phishing, SIM swaps, account recovery fraud, and physical-world intimidation.
The implication for SaaS executives is straightforward: your attack surface is now graph-shaped (identities, tokens, workflows, integrations, exports), and the blast radius is determined less by “did auth fail” and more by how much your trusted planes can reach.
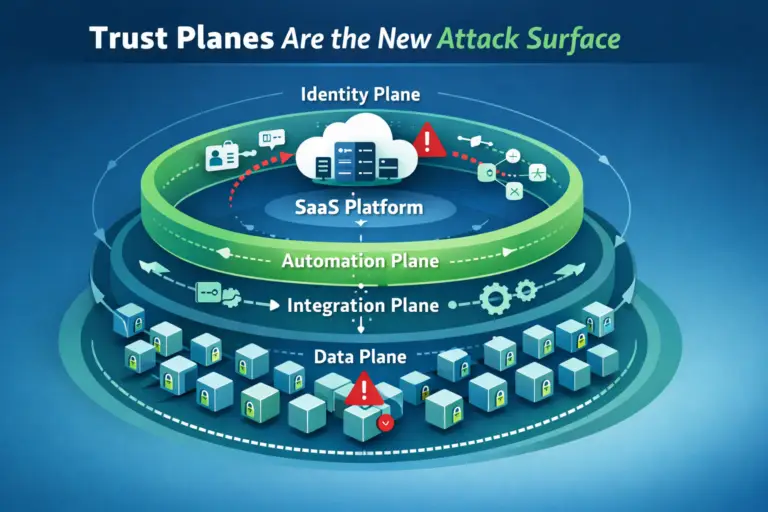
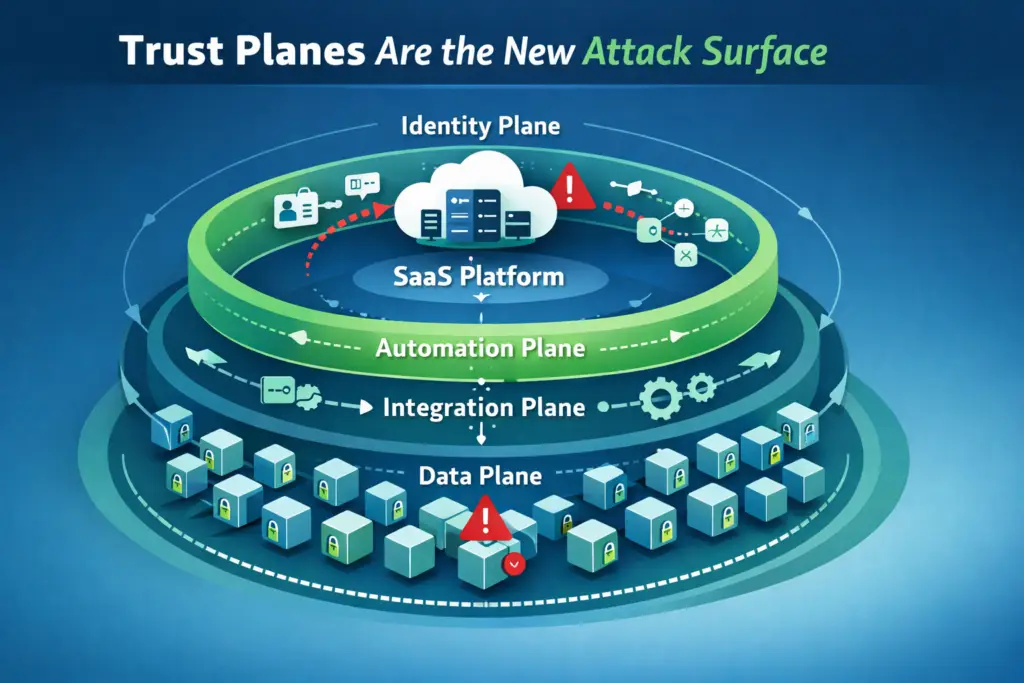
The trust-plane model (use this taxonomy)
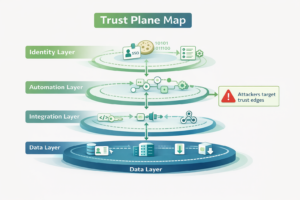
A trust plane is any subsystem that (a) has implicit authorization power, (b) operates at scale, and (c) can be abused to perform legitimate-looking actions.
1) Identity plane
SSO/IdP, MFA, sessions/cookies, SCIM, device posture, privilege elevation, service accounts.
2) Automation plane
Workflow builders, iPaaS, “send email” automations, scheduled jobs, ticket-to-admin flows, CI/CD automations, runbooks.
3) Integration plane
OAuth apps, API keys, partner connectors, webhooks, ETL tools, embedded third-party components.
4) Data plane
Warehouses, multi-tenant databases, object stores, caches, search indexes, analytics exports, backups, staging buckets (“shadow copies”).
The key observation: trust planes are designed to bypass friction. They exist to make work happen quickly. That is exactly why attackers target them.
The goal: make trust-plane abuse boring
Borrowing the same design objective you used in your vendor-containment series, the goal is not “prevent every intrusion.” The goal is:
If a trust plane is abused, the outcome should be boring.
The three levers are:
-
Reduce capability (limit what the abused plane can read/do)
-
Shrink time (limit how long access works)
-
Degrade usefulness (make what leaks less valuable; make tampering noisy)
If your architecture cannot do those three things, trust planes will remain a route to “all-at-once” failure.
1. What trust-plane attacks look like in practice
This is the modern high-impact sequence:

1.1 Initial foothold
Phish, infostealer, malicious OAuth consent, compromised vendor identity, or abused automation.
Session theft is particularly important because it can occur after a user legitimately authenticates, which is why Google and others have been pushing device-bound session concepts (DBSC) to reduce cookie replay value.
1.2 Trust-plane escalation
The attacker moves from “one credential” to “many capabilities” by enumerating connected apps, tokens, service accounts, and workflows.
1.3 Legitimate-looking bulk
The attacker exports reports, syncs datasets, triggers ETL jobs, or queries aggregated stores using valid pathways.
1.4 Monetization
Extortion, fraud, resale, targeted phishing, and downstream compromise.
The operational hallmark is that many actions look legitimate—because they are executed through legitimate trust planes.
2. Trust Plane Containment Checklist (CISO/CTO edition)
Use this as a quarterly review. If you fail a “must-have,” the remediation is architectural: reduce scope, broker access, or isolate sensitive data behind a safer boundary.
A. Identity plane: stop session theft from becoming “full account = full data”
-
Must-have: short session lifetimes for privileged operations; step-up authentication for exports/admin changes.
-
Must-have: phishing-resistant MFA for privileged roles where feasible.
-
Must-have: detections for token replay patterns (new device + privileged action + export).
-
Should-have: device-bound sessions where supported (DBSC) to reduce cookie replay value.
B. Automation plane: treat workflow builders as production systems
-
Must-have: inventory automation assets (owner, purpose, identity used, permissions, logs).
-
Must-have: policy guardrails on external sends (email/webhooks/exports), rate limits, and approval gates.
-
Must-have: no “god-mode” automation principals; each workflow has least-privileged service identity.
-
Why: real-world campaigns have already shown that “trusted cloud automation” can be abused as a delivery channel.
C. Integration plane: scope access to provable, bounded contracts
-
Must-have: no long-lived, broad OAuth scopes “for convenience.”
-
Must-have: per-integration identities with explicit data contracts (fields, tenants, operations).
-
Must-have: separate read vs write; deny bulk by default (pagination caps, export limits, query allowlists).
-
Must-have: a tested kill switch (revoke tokens, disable identities, block paths).
D. Data plane: eliminate “one place that can see everything”
-
Must-have: no unmanaged staging buckets or shadow exports (encrypt, log, lifecycle-delete).
-
Must-have: monitoring for bulk-read patterns and anomalous exports.
-
Strategic requirement: restructure the data layer so compromise of a trust plane cannot assemble cross-tenant plaintext.
This last item is where most programs fail—not because they lack intent, but because the architecture makes bulk plaintext the default.
3. Where architecture changes the outcome
Controls matter. But the durable differentiator is whether your system has a universal plaintext surface area.
If your SaaS runs on a centralized multi-tenant store that must decrypt and process everyone’s data in a shared context, then any sufficiently privileged trust-plane abuse (identity, automation, integration) eventually becomes a bulk-exfiltration opportunity.
This is precisely why “vendor compromise becomes your compromise” keeps recurring, and why incidents that are “not your breach” still produce customer harm.
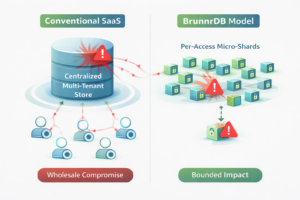
The BrunnrDB framing question
When a trust plane is abused, what is the maximum plaintext an attacker can assemble?
-
In conventional architectures, that answer often trends toward “a lot,” because the server must retain broad decryption and query capability.
-
In BrunnrDB’s model, the answer is designed to stay small:
-
Data is encrypted into packages and stored without giving the server universal decryption capability.
-
Decryption/processing happens at the edge for the briefest possible time.
-
Shards are aligned to authorization boundaries, so “valid access” cannot automatically become a platform-wide dump.
-
This is the architectural equivalent of the “make stolen access boring” objective—implemented at the data layer, not only in IAM policy.
4. Practical patterns that reduce trust-plane blast radius (without a full replatform)
If you are not ready to redesign your entire stack, these patterns materially reduce risk:
-
Integration Gateway Pattern
All vendor/integration calls terminate at your gateway (authn/z enforcement, schema/field filtering, rate limits, audit). Vendors never touch the database directly. -
Sanitized Export Product Pattern
Vendors retrieve curated, time-bounded exports with enforced retention—rather than standing access to production data. -
PII/PHI Vault Boundary Pattern
Move sensitive identifiers behind a narrow service boundary. Most integrations only see surrogate IDs. -
JIT Privileged Access Pattern
Break-glass becomes time-boxed elevation with recorded sessions and automatic revocation.
Each pattern shrinks the power of trust planes and converts silent bulk failure into bounded, observable events.
Quick scorecard (use this to evaluate your current exposure)
If you can answer “yes” to these, you are doing containment—not just compliance:
-
Could you disable any major integration (and revoke its tokens) in minutes?
-
Do your automations run with least privilege and change control, not “admin because it’s easier”?
-
Are your privileged sessions short-lived with step-up auth for exports?
-
Can you prove there are no uncontrolled shadow copies or unmanaged exports?
-
If one trust plane is abused, is the maximum plaintext exposure bounded by design, not by hope?
Conclusion: trust planes will keep expanding—so your data plane must become less fragile
You cannot run a modern SaaS business without identity, automation, and integrations. Those planes will continue to expand because they are how scale happens.
But you can decide whether trust-plane abuse yields bounded impact or wholesale compromise.
The path forward is to harden each plane—then restructure the data layer so the server never has enough context (cryptographically or structurally) to turn one compromised pathway into an “all customers” event.
Bibliography and internal cross-links
1. Verizon. “2025 Data Breach Investigations Report: Executive Summary (PDF).” May 5, 2025. https://www.verizon.com/business/resources/reports/2025-dbir-executive-summary.pdf
2. Check Point Research. “Phishing campaign leverages trusted Google Cloud automation capabilities to evade detection.” Dec 22, 2025. https://blog.checkpoint.com/research/phishing-campaign-leverages-trusted-google-cloud-automation-capabilities-to-evade-detection/
3. Malwarebytes. “Phishing campaign abuses Google Cloud services to steal Microsoft 365 logins.” Jan 6, 2026. https://www.malwarebytes.com/blog/news/2026/01/phishing-campaign-abuses-google-cloud-services-to-steal-microsoft-365-logins
4. Ledger Support. “Global-e Incident to Order Data – January 2026.” https://support.ledger.com/article/Global-e-Incident-to-Order-Data—January-2026
5. The Register. “Ledger confirms customer data lifted after Global-e snafu.” Jan 6, 2026. https://www.theregister.com/2026/01/06/ledger_globale_breach/
6. Google Workspace Admin Help. “Prevent cookie theft with session binding (beta).” https://support.google.com/a/answer/15956470?hl=en
7. Mimir Security Blog. “Vendor Breach Containment: Making Integrations Safe Even When They Get Popped.” Dec 22, 2025. https://www.mimirsec.com/2025/12/22/vendor-breach-containment-making-integrations-safe-even-when-they-get-popped/
8. Mimir Security Blog. “The Hidden Risk in Cloud Databases: When a Vendor Breach Becomes Your Breach.” Oct 30, 2025. https://www.mimirsec.com/2025/10/30/the-hidden-risk-in-cloud-databases/
9. Mimir Security Blog. “Sharding to Contain the Blast Radius of Data Breaches.” Dec 5, 2025. https://www.mimirsec.com/2025/12/05/sharding-to-contain-the-blast-radius-of-data-breaches/
10. Mimir Security Blog. “Protecting Data-In-Use in the Cloud: A Pragmatic Philosophy.” Nov 24, 2025.